Crypto Hot Wallets 101
Key Takeaways:
- Hot wallets are the “operational layer” of crypto designed for high-velocity transactions, whereas cold wallets should serve as your impenetrable vault for long-term holdings.
- Choosing between custodial (exchange-managed) and non-custodial (user-managed) wallets determines whether you prioritize convenience and recovery or total control and self-responsibility.
- Most losses occur not through blockchain failure, but during the “signing” process in internet-connected environments where phishing sites and malware subvert user intent.
- Modern 2026 infrastructure is rapidly moving toward Multi-Party Computation (MPC) and Account Abstraction, which replace risky seed phrases with secure biometric and social recovery.
- Safe participation in the 2026 market requires the regular use of “burner” wallets for new protocols and frequent auditing of token permissions via revocation tools.
Cryptocurrency ownership has crossed the one billion user mark globally, and for the vast majority of those users, the gateway to that ownership is a hot wallet. Whether you are swapping tokens on a decentralized exchange, minting an NFT, or sending stablecoins across borders, a hot wallet is almost certainly the tool you are using to do it. Understanding exactly what a hot wallet is, how it works under the hood, and where its risks lie is not optional knowledge for anyone managing digital assets. It is foundational.
This guide walks through everything you need to know: the technical architecture behind hot wallets, the major providers shaping the market today, the threat vectors that make them dangerous, and the security practices that can protect your funds.
What Is a Hot Wallet?
A hot wallet is a cryptocurrency wallet that maintains a persistent connection to the internet. It stores and utilizes cryptographic private keys on an online device, whether that is a desktop browser, a mobile phone, or an exchange account. This permanent connectivity is the single characteristic that separates it from a cold wallet, which keeps private keys entirely offline in what is often called an air-gapped environment.
The global crypto wallet market was valued at USD 12.59 billion in 2024 and is projected to reach USD 100.77 billion by 2033, growing at a compound annual growth rate of 26.3%, according to industry research. Hot wallets commanded 56% of that market share in 2024. Yet by transaction volume, their dominance is even more pronounced. Stablecoin settlements alone exceeded $4 trillion from January through July 2025, an 83% year-over-year increase, and virtually all of that activity flowed through internet-connected wallets.
The reason is straightforward: cold wallets are secure, but they are slow and cumbersome. Hot wallets are fast, frictionless, and always ready. They are the operational layer of the crypto economy, the tool you use to actually move and deploy capital. Cold wallets are the vault where you store it.
This distinction is the most important framework for thinking about hot wallets: they are built for activity, not custody. Treating them as anything other than that is where most people get into trouble.
The Two Models: Custodial vs. Non-Custodial
Before going further, it helps to understand the two fundamentally different types of hot wallets, because they carry very different risk profiles.
Custodial Hot Wallets
Custodial wallets are operated by centralized exchanges such as Binance, Kraken, and Coinbase’s exchange platform. When you hold funds on one of these platforms, you do not actually possess the private keys. The exchange holds them on your behalf, and you hold an internal balance record. This model is familiar and easy to use. It supports standard account recovery, such as resetting a forgotten password via email. The tradeoff is counterparty risk: if the exchange is hacked, becomes insolvent, or freezes your account under regulatory pressure, your access to those funds is entirely contingent on the platform’s health and goodwill. The collapse of FTX in 2022, which left millions of users unable to access billions in assets, remains the defining example of custodial risk in practice.
Non-Custodial Hot Wallets
Non-custodial wallets place the private keys directly in your hands. Applications like MetaMask, Phantom, and Trust Wallet generate and store keys locally on your device. You become your own bank. There is no third party that can freeze your funds or go bankrupt and take your assets with them. The tradeoff is that the entire burden of security falls on you. If you lose your seed phrase or your device is compromised by malware, there is no customer support line to call. The funds are gone, permanently, because no central authority can reverse a transaction on an immutable blockchain ledger.
Both models have a place in a well-structured digital asset strategy. Custodial accounts are appropriate for casual users who prioritize convenience and are comfortable trusting institutional custody. Non-custodial wallets are the right tool for anyone who takes self-sovereignty seriously and is willing to do the work of securing their own keys.
How Hot Wallets Actually Work
When a user sends funds or interacts with a smart contract through a non-custodial hot wallet, a specific sequence of technical events occurs that reveals exactly where the vulnerabilities lie.
First, the user initiates the transaction by clicking confirm inside a decentralized application. The dApp constructs an unsigned transaction object containing the recipient address, the function being called, the amount, and the maximum gas fee the user is willing to pay.
Second, the hot wallet software receives this unsigned transaction and uses the locally stored private key to mathematically sign it. This signing process occurs inside the active memory of an internet-connected operating system. This is the moment of maximum vulnerability in the entire transaction lifecycle.
Third, once signed, the transaction is broadcast to a blockchain node via a Remote Procedure Call (RPC) endpoint. From there it enters the public mempool, where it waits for a validator to include it in the next block.
The blockchain cryptography at the core of this process is not the weak point. The weakness is the environment in which signing happens. If malware is monitoring the device, or if the user has been tricked into visiting a phishing site that mimics a legitimate DeFi protocol, the hot wallet will apply a valid signature to a malicious transaction. The cryptography works exactly as intended. The user’s intent has simply been subverted before the wallet ever sees the transaction. According to blockchain analytics firm Chainalysis, private key compromises accounted for 43.8% of all stolen cryptocurrency in 2024, a figure that underscores just how central the signing environment is to overall security.
The Major Players in the Hot Wallet Market
The hot wallet landscape has matured into a competitive ecosystem segmented by platform type and blockchain compatibility. Understanding the leading providers helps illustrate both the range of options available and the ecosystem dynamics that drive adoption.
MetaMask
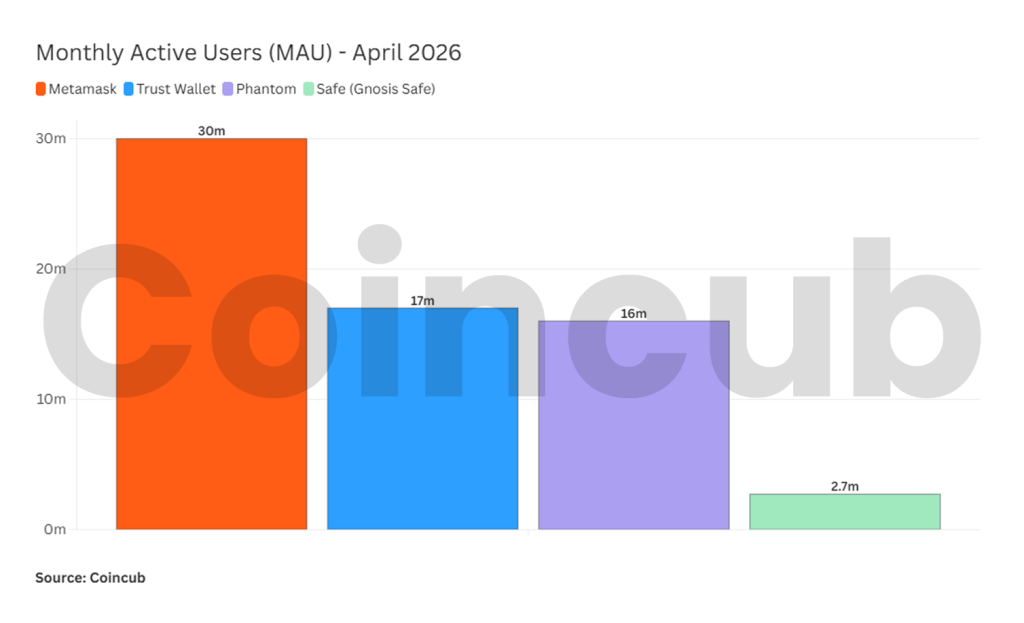
MetaMask, developed by ConsenSys, remains the dominant browser extension wallet for Ethereum and all EVM-compatible networks, including Layer-2 chains like Polygon, Arbitrum, Optimism, and Base. By early 2025, MetaMask reported approximately 30 million monthly active users, a roughly 55% increase from late 2023. Its built-in token swap functionality had generated around $325 million in cumulative revenue by 2025. MetaMask’s near-universal integration across decentralized applications makes it the de facto entry point for anyone engaging with the Ethereum ecosystem.
Its dominance also makes it the primary target for phishing campaigns. MetaMask’s historical reliance on “blind signing,” where users approve complex hexadecimal transaction data without a plain-language summary of what is actually happening, has been the source of significant retail losses when users interact with malicious contracts.
Trust Wallet
Trust Wallet, acquired by Binance in 2018, is the leading mobile-first self-custody wallet, crossing 220 million total users by the end of 2025 and capturing an estimated 35% of the global self-custody market. Unlike MetaMask, Trust Wallet supports over 100 blockchains natively, making it the go-to option for users holding diversified portfolios spanning Bitcoin, Ethereum, Solana, and Cosmos. The wallet’s integrated security scanner reportedly prevented over $191 million from being routed to known scam addresses in 2025.
Phantom
Phantom was built originally for the Solana blockchain, optimized for its high-speed, low-fee transaction environment. Its seamless NFT management and native swap features helped it reach approximately 15 to 17 million monthly active users by mid-2025, representing roughly a five times year-over-year increase driven largely by Solana’s DeFi and memecoin activity. Phantom processed over $20 billion in annual swap volume in 2024 and secured a $150 million Series C funding round in January 2025 at a $3 billion valuation. The wallet has since expanded support to Ethereum, Polygon, and Bitcoin, but its design remains fundamentally optimized for the Solana ecosystem.
Smart Contract Wallets
At the frontier of hot wallet architecture are smart contract wallets, sometimes called smart accounts. Platforms like Argent and Safe (formerly Gnosis Safe) abandon the traditional single-private-key model entirely. Instead, the user’s account is itself a programmable smart contract deployed on the blockchain.
Smart contract wallets enable “social recovery,” a mechanism that distributes recovery access across trusted contacts, hardware devices, or designated security services. If a user loses access, a quorum of these guardians can collectively authorize restoration to a new device, eliminating the catastrophic single point of failure that the seed phrase represents. These wallets can also enforce daily spending limits, require multiple signatures for high-value transfers, and automate account freezing protocols. They represent the architectural bridge between the convenience of hot wallets and the security standards of institutional cold storage.
The Threat Landscape: Where Hot Wallet Losses Actually Come From
Hot wallets exist in an extremely adversarial environment. Approximately $2.2 billion was stolen from crypto platforms and users in 2024, a 21% year-over-year increase according to Chainalysis. The threat landscape accelerated further in 2025: total stolen funds approached $2.5 billion in just the first half of the year, and by year’s end, losses from hacks and exploits exceeded $3.4 billion. Individual wallet attacks surged to 158,000 recorded incidents affecting at least 80,000 unique victims in 2025, with wallet compromises accounting for roughly $1.71 billion in losses in the first half of the year alone.
Understanding where those losses come from is the first step toward preventing them.
Phishing and Wallet Drainers
Wallet drainers are commercially packaged malicious scripts deployed on fraudulent websites. Victims are typically funneled to these sites through fake airdrop campaigns, hacked social media accounts of prominent crypto figures, or search engine ads designed to mimic legitimate platforms. When a user connects their wallet to the malicious site, the drainer script prompts them to sign a transaction that grants the script’s smart contract unlimited access to their tokens, often disguised as a routine login confirmation or reward claim. In 2023 and 2024, wallet draining services were responsible for over $300 million in direct retail losses, affecting more than 324,000 victims. In the first half of 2025 alone, phishing and drainers extracted over $410.7 million across 132 recorded mass-phishing events.
Infostealer Malware and Clipboard Hijacking
Infostealer malware targets the operating system rather than the blockchain. Variants like RedLine and Raccoon are commonly distributed through pirated software, malicious email attachments, and executable files shared on gaming forums. Once installed, these programs scan browser extensions and local storage for wallet configuration files and seed phrases stored in plaintext documents or notes applications.
Clipboard hijacking is a particularly insidious variant. When a user copies a destination wallet address, the malware detects the clipboard activity and instantly replaces the copied address with one controlled by the attacker. Cryptocurrency addresses are long, randomized strings that users rarely read character by character. If the user fails to verify the full address before confirming, the funds go directly to the attacker, and the transaction is irreversible.
Supply Chain Attacks
A supply chain attack compromises a trusted software provider, turning a legitimate application into a malicious delivery mechanism. The user does nothing wrong. The tool they trusted betrays them.
In August 2022, Slope Wallet on Solana suffered a breach that drained 9,229 wallets, resulting in approximately $4.1 million in losses. Forensic analysis revealed that a debugging integration with a third-party application monitoring service called Sentry was inadvertently logging users’ private keys and seed phrases in plaintext. The data was transmitted to a centralized, unencrypted logging server over several weeks. Attackers who accessed that server had direct access to the cryptographic keys of 6,811 unique wallets.
In February 2025, the centralized exchange Bybit suffered the largest single crypto heist in history: $1.5 billion in Ethereum stolen from its hot wallet infrastructure. State-sponsored hackers linked to North Korea compromised a developer’s computer that managed the exchange’s multi-signature transaction interface. Malicious JavaScript was injected into the frontend, secretly altering transaction parameters. When Bybit operators performed a routine transfer, they unknowingly signed a transaction that routed 401,000 ETH directly to attacker-controlled addresses. North Korean threat actors stole a record $2.02 billion in total across 2025, according to Chainalysis, accounting for 76% of all centralized service compromises through supply-chain manipulation and false-identity fraud schemes.
Practical Hot Wallet Security: The Non-Negotiables
The threat landscape is severe, but it is not unmanageable. The following practices represent the minimum viable security posture for anyone using a non-custodial hot wallet.
- Use burner wallets for new protocols. Never connect a wallet holding significant funds to an unverified or newly launched decentralized application. Generate a temporary address, fund it with only the exact amount needed for the specific transaction, and interact exclusively from there. If the contract is malicious, only the burner balance is at risk.
- Segregate assets by risk level. A hot wallet should function like a physical leather wallet: carry only what you need for daily activity or active trading. The bulk of your portfolio belongs in a hardware cold wallet, fully disconnected from any network.
- Revoke token approvals regularly. When you interact with a decentralized exchange or NFT marketplace, you grant that protocol’s smart contract permission to move your tokens. Interfaces frequently default to requesting infinite allowances to save future gas fees. If that protocol is later compromised, that pre-existing approval can be exploited to drain your wallet without requiring a new signature. This is not optional maintenance. It is an essential part of ongoing wallet hygiene.
- Source your wallet software correctly. Never find a wallet by clicking a search engine result or a sponsored ad link. Navigate directly to the official project website or use the verified link from the project’s official social media. Fake wallet downloads are a primary vector for credential theft.
- Write your seed phrase on paper, not pixels. During wallet setup, write your seed phrase on physical paper or, better, stamp it into a fireproof metal backup. Never photograph it, type it into a notes app, or paste it anywhere. If your device is compromised by an infostealer, every digital file is a potential target.
The Future: Removing the Seed Phrase Entirely
The fundamental weakness of traditional hot wallets is their reliance on a single cryptographic element: the seed phrase. Lose it and access is gone permanently. Expose it and everything is stolen instantly. The industry is actively building toward architectures that eliminate this vulnerability entirely.
Multi-Party Computation (MPC) addresses this by splitting the private key into cryptographic shards distributed across multiple locations, such as a mobile device, a cloud backup, and the wallet provider’s servers. Signing a transaction requires a predefined threshold of these shards to collaborate mathematically. The complete private key never exists in any single location, rendering device-level infostealers significantly less effective. Coinbase has integrated MPC into its Wallet-as-a-Service infrastructure, and consumer wallets like ZenGo use biometric authentication combined with MPC to eliminate the seed phrase from the user experience entirely.
Account Abstraction, formalized in the Ethereum ERC-4337 standard launched in 2023, goes further by changing how accounts function at the protocol level. Rather than signing standard transactions, users of smart accounts create structured UserOperation objects that are processed through a specialized offchain pipeline before being submitted onchain. This enables gas sponsorship by applications, batch execution of multiple operations in a single signature, programmable spending limits enforced at the blockchain level, and native support for biometric authentication via device secure enclaves and passkeys.
The convergence of MPC, Account Abstraction, and emerging standards like EIP-7702 points toward a future where interacting with the blockchain will feel indistinguishable from using a conventional banking application. The seed phrase, and the catastrophic risks it carries, will be an architectural artifact of an earlier era.
Conclusion: The Core Principle Has Not Changed
Technology changes, ecosystems expand, and security standards improve, but the core principle governing hot wallet use is the same as it has always been: treat a hot wallet the way you treat the cash in your pocket. Carry only what you need for the near term. Keep the rest somewhere safer.
Hot wallets make the crypto economy function. They are the transaction layer that connects user capital to decentralized applications, cross-border payments, and onchain financial services. Their convenience is genuine and necessary. So is the risk that comes with it. Understanding both, and acting accordingly, is the starting point for responsible self-custody.
Frequently Asked Questions (FAQs)
What is the best crypto hot wallet?
MetaMask and Phantom lead for ecosystem support, but in 2026, Safe (formerly Gnosis Safe) is widely considered the best for security due to its smart account features. For mobile users, Trust Wallet offers the best multi-chain experience. The right choice depends on your specific chain and security needs.
What is a hot wallet for crypto?
A hot wallet is a cryptocurrency storage application that remains connected to the internet. It enables fast transactions and seamless interaction with decentralized applications (dApps). While highly convenient for active traders, its constant online status makes it more vulnerable to hackers and malware than offline cold storage options.
What are the top 5 crypto wallets?
The top 5 crypto wallets in 2026 are MetaMask, Phantom, Trust Wallet, Ledger, and Safe. These are selected based on their robust security protocols, multi-chain compatibility, and widespread integration with DeFi platforms. They offer a mix of hot, cold, and smart contract storage solutions for all users.
Is a hot or cold crypto wallet better?
A cold wallet is better for long-term security, as it keeps your private keys offline. A hot wallet is better for daily convenience, enabling instant trading and dApp connectivity. For optimal safety, use a hybrid strategy: keep your savings cold and only your active capital in a hot wallet.




