12 Crypto Hacks That Made History
Summary
- Most damage starts with keys or validators.
- Bridges mix speed and trust, so they stay fragile until proofs and governance harden.
- Multisig works only when signer separation and staged flow are enforced.
- Fast attribution and coordinated freezes now change outcomes in real time.
- One giant breach can still define a year.
The word “hack” gets used for everything in crypto. A hack means someone gained unauthorized control over keys, validator sets, or smart-contract logic and moved funds. If it was an insider or a collapse drain, it still counts when users lost money the same way they would in an external breach. Rugs and market manipulation sit out, especially since they are so normalized these days and there is little to what you can do if you get rugged in a platform such as Pump Fun. Phishing that only hits a few wallets sits out unless it was the entry point for a bigger treasury hit. Amounts are valued at the time of the theft, not today’s price. That keeps the story about security, not about bull markets.
As such, this content is a walk through the breaches that bent the curve of crypto security. Not every scam. Not every rug. These are the ones that changed how people build, secure, insure, and regulate. We’re talking infrastructure failures (keys and bridges), not “my cousin clicked a link.”
Amounts are at-time USD or BTC so we don’t distort the story with market drift. Where necessary, we’ll say what was reimbursed and how.
1. Mt. Gox (2011-204): $460-$473M in BTC
Before “crypto exchanges” looked like banks with uptime SLAs, there was a PHP site with the world’s BTC flowing through it. Gox wasn’t “hacked once.” It leaked for years. Weak key custody, poor accounting, and no clean separation between customer balances and operational funds left a hole that wasn’t obvious until 2014, when the lights went out. The main lesson was “custody is a business.”
Keys live in procedures rather than folders on servers. Repayments and litigation dragged for a decade, and even partial distributions moved markets because the volumes were that concentrated. The early culture of “ship first, harden later” ended here; professionalized custody began.
This hack turned “security” from a blog promise into a regulated product with audits, segregation of duties, and boring controls.
A man documents Bitcoin crashing from $17.00 to $0.01 in 2011 as the Mt. Gox exchange was hacked. pic.twitter.com/t5UiwJtNXb
— Whale Insider (@WhaleInsider) July 4, 2024
2. Bitfinex (Aug 2016): 119,756 BTC
While Multisig was the buzzword, integration was its weak spot. Bitfinex relied on a partner’s multisig flow that didn’t behave like the mental model suggested under real pressure. Funds vanished; users ate a haircut; the exchange issued BFX IOU tokens and later made people whole.
Years later, U.S. authorities seized large chunks as laundering cases unfolded. This is where a lot of teams learned the ugly truth: you don’t “have multisig,” you design and operate it. Thresholds, signer separation, change control on wallet software, and staged withdrawal policies are THE thing. The other lesson was that you can improvise capital structure in an emergency, but you can’t improvise controls. Security is an end-to-end process across vendors, code, and humans.
3. Coincheck (Jan 2018): $532-$534M
A hot-wallet breach moved half a billion in NEM while staff slept. Coincheck didn’t have serious cold storage for that asset and didn’t have a multi-signature gate in front of the NEM wallet. Japanese regulators arrived, wrote checks in red ink, and the exchange reimbursed customers from reserves.
The rest of the industry took the hint that hot is for flow, cold is for everything else. Segregate assets so a single wallet compromise can’t take the house. It was the first time a national watchdog put a mass-market exchange on rails and the market didn’t die; it just got safer and more boring by design. This hack standardized “majority cold, minority hot” for CEXs in a way blog posts never could.
4. Poly Network (Aug 2021): $610-$611M
A cross-chain logic bug let a stranger reroute value across Ethereum, BSC, and Polygon. Then the stranger started sending it back. We got public negotiation on-chain, a $500K bounty, and a dozen think pieces arguing about whether intent absolves theft. Tether froze a chunk; the rest dribbled back over two weeks.
The bigger point was that bridges are not “just contracts.” They’re complex distributed systems with proof schemes and trust assumptions that can fail in weird ways. Poly normalized two things: the idea that nine-figure “white hat” returns are possible, and that bridges need bank-grade review of message validation, not just code style. This hack made everyone treat cross-chain code like financial market infrastructure. Or it should have.
5. Wormhole (Feb 2022): $320-$325M
Signature verification failed on the Ethereum-Solana bridge and 120,000 wETH appeared without backing. Then Jump stepped in and replaced the funds, immediately. Users didn’t eat the loss, actually, the sponsor did. This drew a huge line.
“DeFi” can still have a lender of last resort if a strategic backer’s exposure is existential. The technical postmortems focused on signature paths and verification logic; the business takeaway was louder. If you’re critical infrastructure, then someone needs to be financially on the hook for catastrophic failures or your users are playing roulette. Interop is only as safe as its verification path. And occasionally, the safety net is a market maker’s balance sheet.
6. Ronin / Axie Infinity (Mar 2022)
Five of nine validators were enough to approve fake withdrawals. A gas-free RPC made it slick, while social engineering did the rest. At the time, it was the largest theft in crypto, and it hit a consumer gaming ecosystem with retail users in developing countries. Sky Mavis raised capital and reimbursed users, but the hammer fell elsewhere. U.S. authorities later tied it to North Korea’s Lazarus Group.
For security teams, Ronin was the graph that made every slide deck. “Decentralized” on paper can still be a small Slack room with a handful of keys. Thresholds, independent validators, and key ceremony hygiene aren’t academic. This is what happens when they aren’t real. Validator centralization plus social engineering equals a bank with one guard.
7. BNB Chain Token Hub (Oct 2022): $569-$570M
Forged proofs minted 2M BNB. The chain paused. Funds got frozen on exchanges and other networks, but the attacker still walked with a meaningful slice. The lesson was that proof systems are part of your attack surface. If a proof can be forged, your bridge mints money. That’s not “a bug,” a more accurate description would be a commercial-bank crisis on a blockchain.
Binance introduced governance changes and emergency playbooks, and the industry discovered that bridge proofs belong in board decks along with audits. Bridges can be like banks without branches. Their paperwork has to be bulletproof.
8. FTX Post-Collapse Drain (Nov 2022): $477-$482M
While the bankruptcy lights flickered, wallets emptied. Whether you think “hack” or “insider,” the lesson is almost identical. Crisis IS part of security. If your runbook doesn’t say exactly who can move what, how you freeze, and who talks when comms go dark, the worst hour writes your runbook for you.
FTX proved that technology is not enough. Governance and emergency procedures are security controls. You can have two-factor authenticator on every account and still lose if your organization chart melts. Custody is crisis discipline to say the least.
9. DMM Bitcoin (May 2024): 4,502.9 BTC
Keys touched the wrong surface, and… BTC walked. Japan’s National Police Agency, the FBI, and DoD’s DC3 published a joint identification. TraderTraitor, a DPRK cluster, was responsible. Tether blocked a slice; the company raised capital to cushion users. The laundering flowed across multiple chains.
This was a very modern playbook. A server-side compromise, session hijack, then multi-chain obfuscation. The technical moral showed that servers are not safes. Treat signing paths like nuclear material (literally). Public, fast, cross-border attribution became the new normal, and it helps defenses in flight. This hack nailed down the classical model. An off-chain breach, an on-chain drain, and a cross-chain wash. The public responded, and it was a multi-agency attribution.
10. WazirX (Jul 2024) – $230M
India’s biggest domestic exchange watched a “main trading wallet” drain despite a custody vendor and a multisig setup. The post-mortems point to a compromised multisig path and pre-positioning via privacy infrastructure. The team published a day-by-day timeline. India’s market saw a trust shock. Users finally learned that multsig isn’t magic.
The controls that actually matter are how you enroll signers, rotate them, stage large withdrawals, and stop a compromised path before it empties a primary wallet. This was a governance and op-sec problem with a very public blast radius. “We use multisig” must not be a talisman. Humans, providers, and processes decide outcomes.
11. Bybit (Feb 2025): $1.4-$1.5B in ETH
Four hundred thousand ETH moved in minutes (read that again, slowly). The FBI published a PSA less than a week later naming the actor: North Korea, TraderTraitor. Blockchain analysts traced the movement across dozens of addresses, into DEXs, through bridges, and into mixers. Industry write-ups focused on the laundering speed and the attribution. Academic work dug into the how. They showed that a cold-to-warm transfer flow compromised by UI deception and blind-signing, with a delegatecall pivot that let attackers rewrite a wallet’s implementation address mid-approval.
Lazarus Group just connected the Bybit hack to the Phemex hack directly on-chain commingling funds from the intial theft address for both incidents.
Overlap address:
0x33d057af74779925c4b2e720a820387cb89f8f65Bybit hack txns on Feb 22, 2025:… pic.twitter.com/dh2oHUBCvW
— ZachXBT (@zachxbt) February 22, 2025
That turns “we have multisig” into theater if your signers can’t see what they’re really authorizing. The exchange stabilized liquidity via partner loans and tried to calm the market, while defenders compared notes in real time. This was the new apex case. Proper modern social engineering plus UI-level misdirection plus fast public attribution. The theft was fast, the attribution was faster. It also forced everyone to treat transaction interfaces as part of key management, not a cosmetic layer.
12. Nobitex (Jun 2025): $90M
Not every heist is about profit. Predatory Sparrow claimed responsibility, siphoned funds, and then parked them in vanity addresses that nobody could ever spend (addresses with anti-regime slogans embedded in them). This was more about sending a message rather than laundering.
It came as part of a broader run of politically-motivated ops and it pushed exchanges to think about threat models that aren’t just “get rich.” You also plan for “make a point,” and that changes response priorities: comms, user protection, and law-enforcement handoff look different when money is being burned in public. This hack finally showed how geopolitical operations can target crypto venues to signal if not cashing out.
BREAKING 🔴🔴🔴
Israeli-linked hacker group “Predatory Sparrow” wiped out 95% of assets on Iran’s Nobitex crypto exchange.
Nobitex was reportedly used by Tehran to evade sanctions through crypto. Wallet balances plunged from $1.8 billion to just $100 million. pic.twitter.com/vaKoRwHHRV
— Open Source Intel (@Osint613) June 18, 2025
Where We Stand: What Our Data Shows
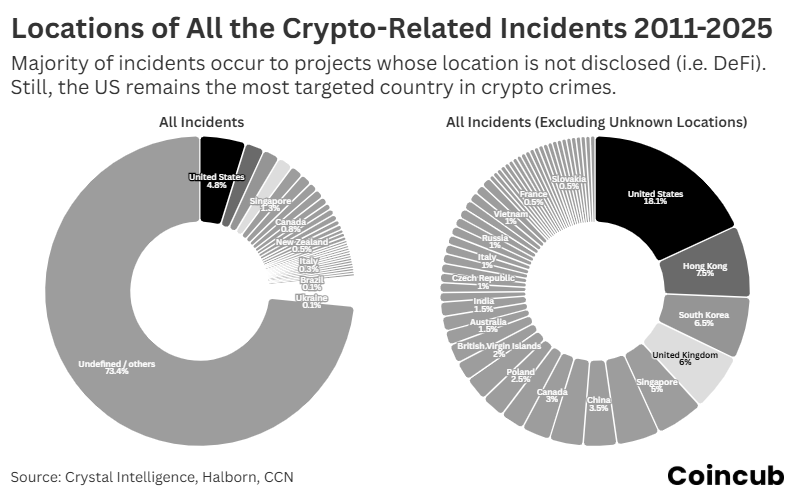
Location counts look decisive at first. They aren’t. The biggest slice is “unknown/undefined,” because a lot of DeFi code lives everywhere and nowhere. When you remove unknowns, the U.S. leads, then Hong Kong, the U.K., Singapore, and South Korea. That mirrors liquidity, market-maker presence, hosting, and banking rails. Attackers follow flow. If activity, fiat ramps, and compliance teams sit in a hub, so does risk. Read this chart as a map of capital concentration and service density, not as a morality ranking for countries. Teams that operate from these hubs need stricter key segregation, signer separation across entities, and faster freeze playbooks, because response windows are shorter where liquidity is deepest.
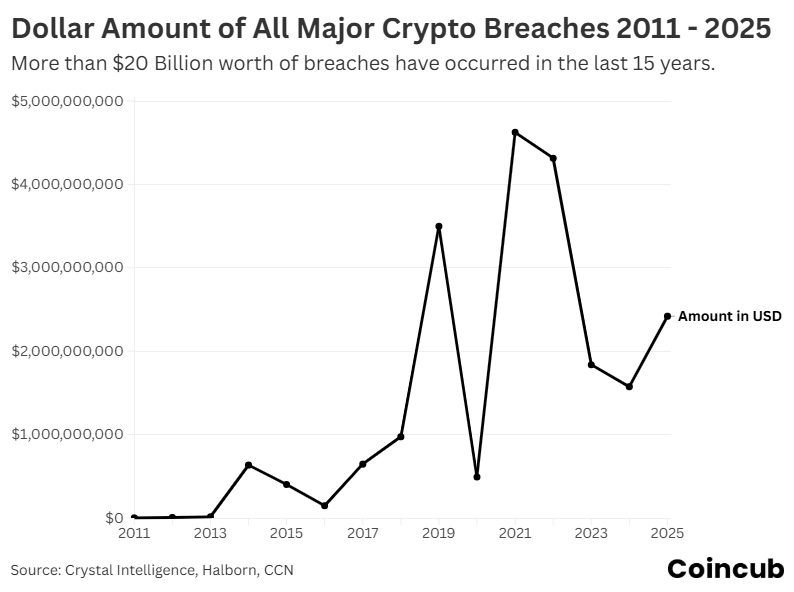
This graph tells the story better than any headline. A quiet start. Then the 2019-2020 climb as centralized venues scaled faster than controls. A spike in 2021-2022 when bridges and DeFi plumbing moved serious value. A pullback in 2023-2024 after insurers, auditors, and law enforcement tightened the screws and teams finally implemented boring fixes like staged withdrawals and proof hardening. 2025 ticks up again almost entirely because of one record CEX drain. That is the pattern you plan for. New rails launch, attackers arrive first, defenders catch up a year later, and a single outlier can still bend a whole year. If you run infrastructure, budget for “the year after launch,” not launch day. That is when copycats test your edge cases.
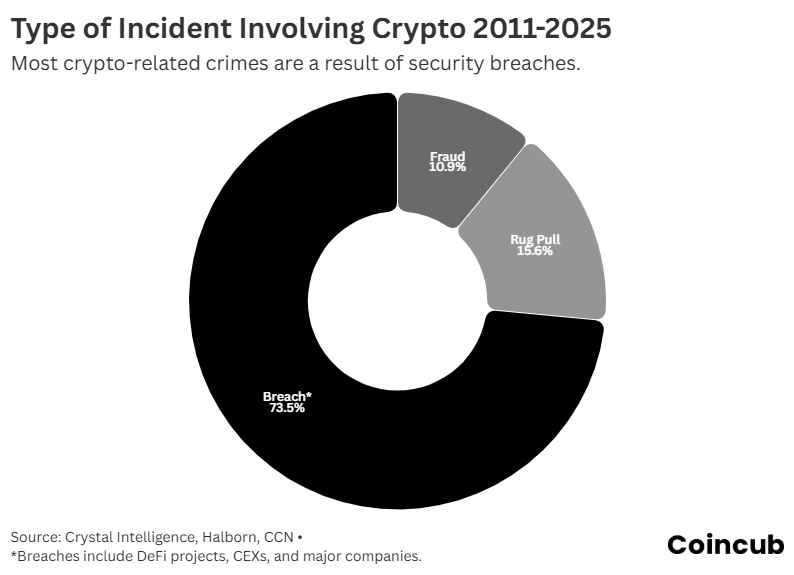
Roughly three-quarters of incidents are security failures: keys, bridges, app-layer logic. Rugs and classic frauds are noisy but smaller once you filter meme seasons and tiny caps. This aligns with what we just walked through. Treasury lives in key paths and interoperability routes, so that is where nine-figure losses start. The control stack that actually moves this pie chart. Always isolate keys from servers, distribute signers across people and orgs, require staged approvals on size and destination, and treat bridge proofs like bank paperwork with independent verification. Add user-facing protections that kill blind-signing. If your signer cannot explain the action in plain language, you are one click away from being a dot on this chart.
Patterns You Can’t Ignore
Keys go missing more than code breaks. Bridges keep getting picked because they mix trust, complexity, and speed. “Decentralized” often resolves to a few people with the same calendar. On the bright side, recovery and coordination improved. Cross-border ops like HAECHI froze hundreds of wallets and recovered meaningful funds across dozens of countries, and private backstops occasionally made users whole. State-linked crews continue to scale, and they outsource pieces of the killchain to freelancers and OTC brokers, blending old-world and on-chain tradecraft.
Words decide who pays and how fast. If it’s an external exploit, you ship patches, rotate keys, and talk bounties and counter-laundering. If it’s insider abuse or governance failure, you talk access control, segregation of duties, audit trails, and criminal liability. Courts and regulators read the nouns first. That shapes restitution timelines and the compliance fallout.
Twitter threads are not evidence. The way you make a fix you can ship is to replicate the exploit in a controlled environment. The modern method is all about redeploying the contracts, building one-to-one mappings for addresses hard-coded in bytecode, mirroring storage slots, and then executing the same call sequence with a “hack replay” contract to replicate the exact failure. That surfaces the real dependency, maybe a proxy’s delegatecall, maybe an approval that hides logic behind a clean-looking address, and lets you test defenses. There are limits of course. Replaying things that depend on exact block.timestamp behavior or massive native token balances gets impractical. But for most EVM incidents, this approach turns narrative into proof, and proof into patches.
What Actually Changed
Cold storage must be the default. Multisig is a process rather than a checkbox. Bridge teams moved to stronger proof systems and emergency halts. Law enforcement coordination got very real; public attributions of nation-state crews now arrive in days (used to be years).
The data says the bulk of damage comes from infrastructure-level failures and key compromise, and state-linked groups still operate at scale, but the policy world is finally catching up. Travel-rule alignment, new AML authorities, and a push for compliance-by-design identity stacks that preserve privacy while making forensics and KYC less theatrical. Whether you love that or not, it’s the road we’re on.
If you are a builder, decide what you will never do with keys. Decide who can move what when everyone is tired. Decide how you freeze and how you talk when it hits. Write it down. Test it with people who didn’t write it. Treat UI as part of custody because it is. That means real-time smart-contract validation in the signer, contextual prompts for high-risk functions, and automatic blocklists for known phishing contracts. Move signer teams to geographic and organizational separation. Make HSMs boring, mandatory infrastructure. These can be the reasons you’re still online tomorrow.
And if you’re a user, assume any venue can fail. Keep size in cold storage. Treat new bridges like new banks. Start tiny. Watch liquidity and communications like you watch price. Never blind-sign. Read the function you’re approving, especially anything that sounds like “ownership,” “permit,” or “delegate.” The people who still have their coins after big incidents didn’t trust the brand. Instead they trusted and relied on their habits.
Frequently Asked Questions (FAQ)
What counts as a “hack”?
Incidents where attackers gained unauthorized control of keys, validator sets, or smart-contract logic and moved funds. Inside jobs and post-collapse drains are included when the effect on users and the market matched an external exploit.
Why use “value at the time” instead of today’s price?
Price drift distorts history. A 2014 loss priced at 2025 levels turns a security story into a bull-market story. Using the value at the time keeps the signal clean.
Why are bridges so often in the list?
Bridges join different chains with proofs and message passing. Small flaws create money from thin air. Designs that look safe on paper fail when proofs can be forged or signers are concentrated.
If multisig is everywhere, why do CEX wallets still get drained?
Because the weak link is the signing path and the humans in it. Multisig without strict signer separation, staged approvals, and clear transaction prompts is theater. Blind-signing kills good setups.
What changed after the big hacks?
Cold storage by default. Stronger bridge proofs. Staged withdrawals. Faster cross-border freezes. Private backstops for critical infra. Better, not perfect. Key compromise and validator capture still lead losses.
How do investigators get funds back?
They track flows across chains, flag service addresses, and work with exchanges and stablecoin issuers to block or claw back assets. Results depend on speed, the attacker’s tradecraft, and jurisdiction.
What should a normal user do differently?
Keep size in cold storage. Use hardware signers. Start small on new bridges. Read approvals. Treat venue transparency and crisis communication as part of your risk model.