5 Best Anonymous Crypto Wallets in 2026
Privacy has become the most valuable asset in the digital world. Every card swipe, bank transfer, or blockchain transaction generates data points that can be tracked, analyzed, and monetized. What began as a push for transparency has evolved into a surveillance economy where identity is constantly exposed. Crypto was designed to challenge that idea and restore financial freedom by removing intermediaries and giving people control over their own money.
But the uncomfortable truth is that most cryptocurrencies are not anonymous. Bitcoin and Ethereum record every transaction on public ledgers that anyone can inspect. Addresses may not display names, yet they reveal spending patterns and wallet histories that link back to real users over time. The illusion of privacy disappears the moment data leaves the chain and meets an exchange, wallet provider, or analytics firm.
This growing tension between transparency and autonomy has pushed developers to build tools focused solely on confidentiality. Zero-knowledge proofs, shielded addresses, CoinJoin protocols, and Tor-based connections have become essential features for users who refuse to trade privacy for convenience. Still, tools alone cannot guarantee anonymity. The wrong wallet choice or careless habits can expose identities faster than any blockchain explorer.
What Makes a Wallet “Anonymous” in Practice?
True anonymity in crypto is a structure built from several layers of design and user discipline. A wallet becomes anonymous when it removes custodial oversight, hides identifiable network data, and prevents onchain linkability between transactions. To achieve that, it must blend both technical privacy mechanisms and responsible usage patterns.
An anonymous wallet must never hold user funds or personal data. Non-custodial design means you control the private keys, while the wallet cannot access or freeze assets. Combined with a no-KYC policy, this ensures that no personal identifiers such as email, name, or IP address are tied to your wallet activity. Privacy begins at setup. If you submit identity documents, the anonymity claim is already broken.
Techniques like CoinJoin, PayJoin, coin control, and subaddresses help obscure transaction origins and destinations. CoinJoin merges multiple user transactions into one combined transaction, breaking deterministic links. PayJoin adds randomness to ordinary payments by including the receiver’s input, confusing chain analysis further. Coin control allows users to choose which specific coins to spend, preventing old addresses from revealing full histories. Subaddresses create new receive addresses automatically, making it difficult for observers to group incoming funds.
Even with clean onchain habits, broadcasting transactions through public servers exposes metadata. Privacy-oriented wallets route activity through Tor, giving each transaction a fresh IP identity. Advanced wallets let users connect their own full node, bypassing centralized servers that could log requests or monitor broadcast patterns.
No wallet is perfectly anonymous. Sophisticated chain analysis, poor operational hygiene, or UX simplifications can erode privacy. Some wallets trade convenience for security, while others face regulatory scrutiny in different jurisdictions just to remain truly private.
5 Best Anonymous Crypto Wallets for 2025
Wasabi Wallet 2.x (Bitcoin, Desktop): CoinJoin and Tor Integration
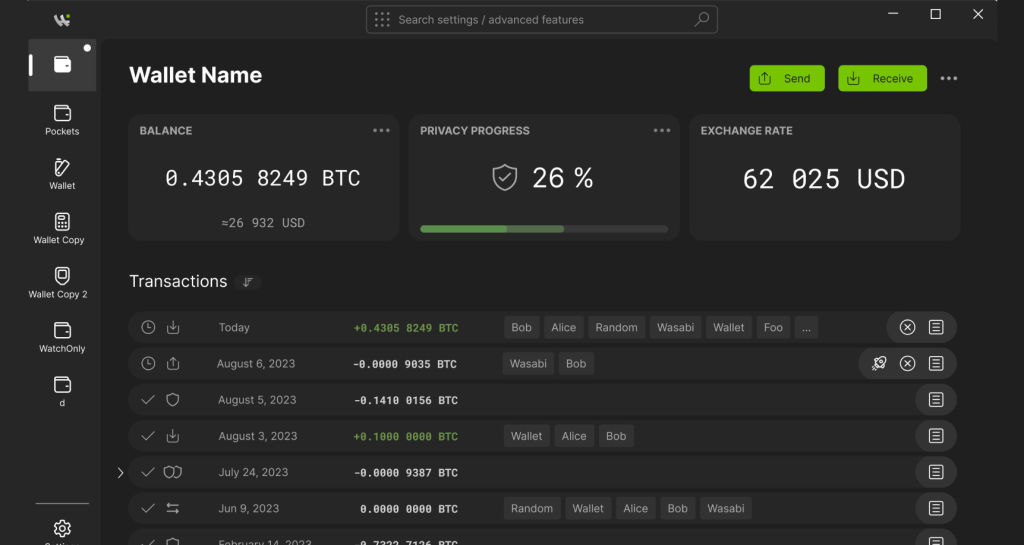
Who it’s for: Bitcoin users who want automated privacy without manual mixing or technical setup.
Wasabi Wallet remains one of the most battle-tested privacy wallets for Bitcoin. The latest 2.x version builds on its WabiSabi CoinJoin protocol, which replaces the earlier equal-output method with a more efficient and private design. Each CoinJoin session combines multiple user transactions into one unified transaction, breaking the deterministic links that blockchain analytics rely on. The coordinator model prevents participants from knowing each other’s identities, while built-in Tor ensures every connection hides its IP address by default.
Wasabi also includes granular coin control, allowing users to decide which UTXOs to spend and which to isolate. This prevents cross-contamination between public and private funds. While a small coordinator fee applies to mixed outputs, the improved structure of WabiSabi reduces costs and wait times compared to older versions.
The open-source codebase is active and regularly audited, maintaining transparency and community trust. However, users should understand that the CoinJoin coordinator still acts as a mediator for transaction aggregation, which introduces a limited trust assumption. Despite this, Wasabi’s consistent development pace and privacy-first design make it one of the strongest Bitcoin options for users who want a balance of automation and control.
Sparrow Wallet (Bitcoin, Desktop): Advanced Coin Control and PayJoin Support
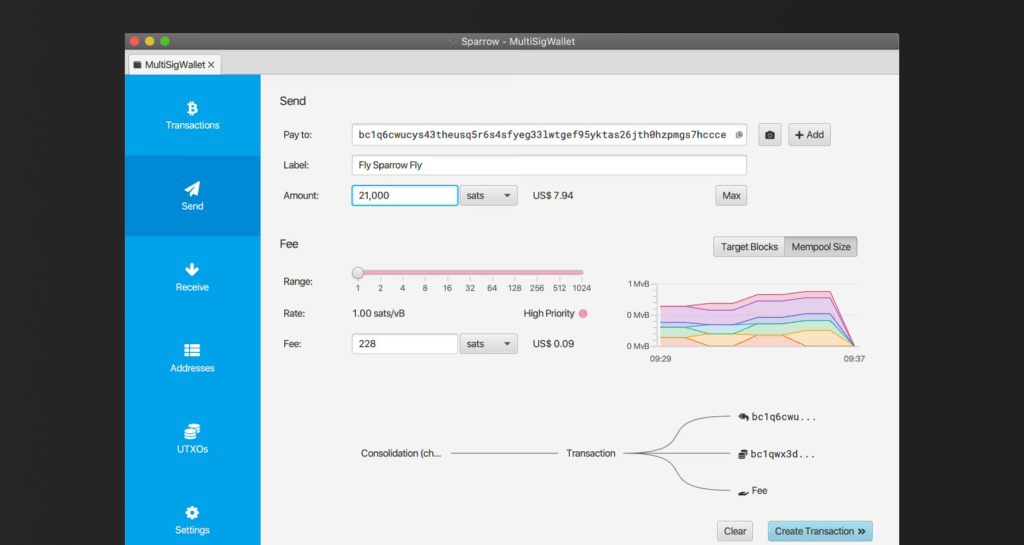
Who it’s for: Experienced Bitcoin users who prefer manual control and precision over automation.
Sparrow Wallet is a power tool for privacy-focused individuals who understand Bitcoin’s transaction mechanics. It offers full PayJoin integration, a method that makes ordinary payments indistinguishable from CoinJoin transactions by including inputs from both sender and receiver. This disrupts heuristic tracing tools that rely on predictable transaction structures.
The wallet also supports manual CoinJoin coordination via Whirlpool or WabiSabi, advanced coin labeling, and built-in Tor routing. Its full-node compatibility gives users the ability to broadcast transactions through their own node, removing the dependency on third-party servers that could log network data.
Sparrow’s interface balances professional-grade analytics with a clean layout, making complex actions like coin labeling and multi-wallet management approachable. However, its depth of options may intimidate beginners. A wrong setting can inadvertently link transactions, so users must understand coin selection and address hygiene.
Community trust around Sparrow is strong, but phishing attempts have targeted new users. Always verify downloads from the official site or GitHub repository, and confirm PGP signatures when possible. When used correctly, Sparrow provides one of the most transparent and controllable paths to Bitcoin privacy available today.
Zashi (Zcash, Mobile): Shielded Transactions and Viewing Key Control
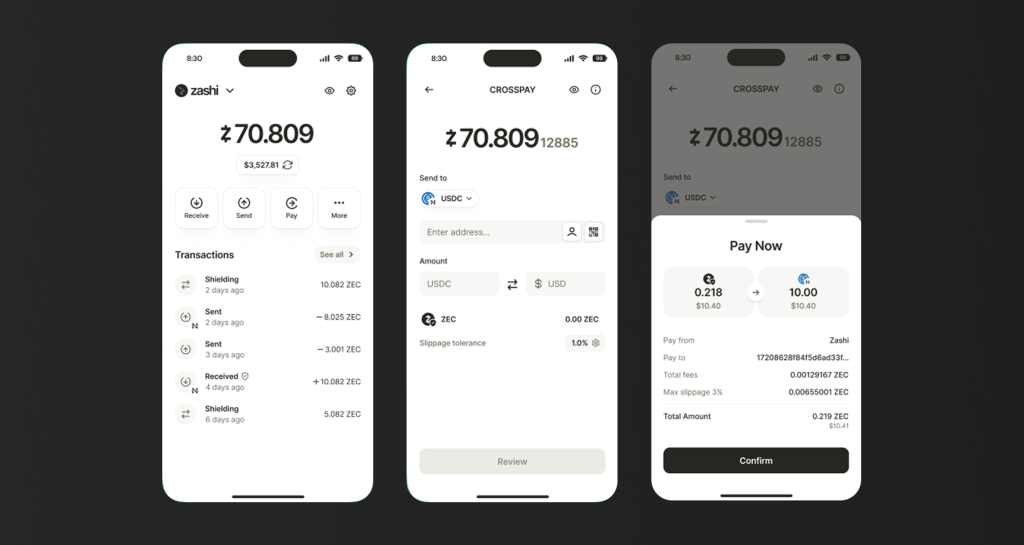
Who it’s for: Mobile users who prioritize transaction privacy through zero-knowledge proofs.
Zashi is the official Zcash wallet developed by the Electric Coin Company. It brings Zcash’s shielded transaction technology to an accessible mobile interface, allowing users to send and receive ZEC privately using z-addresses. These shielded transactions use zero-knowledge proofs to hide both sender and receiver information while still proving transaction validity to the network.
Zashi introduces selective disclosure through viewing keys, which let users share transaction details with trusted parties such as auditors or tax professionals without revealing their entire wallet history. This feature combines accountability with privacy.
The wallet is open source, maintained directly by the Zcash core team, and available for both iOS and Android. It also integrates full Tor connectivity, ensuring transaction broadcasts remain untraceable at the network level.
Regulatory attitudes toward privacy coins remain complex, and some exchanges restrict ZEC trading in certain jurisdictions. However, from a technical standpoint, Zashi represents one of the most mature implementations of shielded payments, enabling true financial confidentiality without sacrificing compliance options when required.
Nunchuk (Bitcoin, Mobile & Desktop): Multisig Security with Privacy Discipline
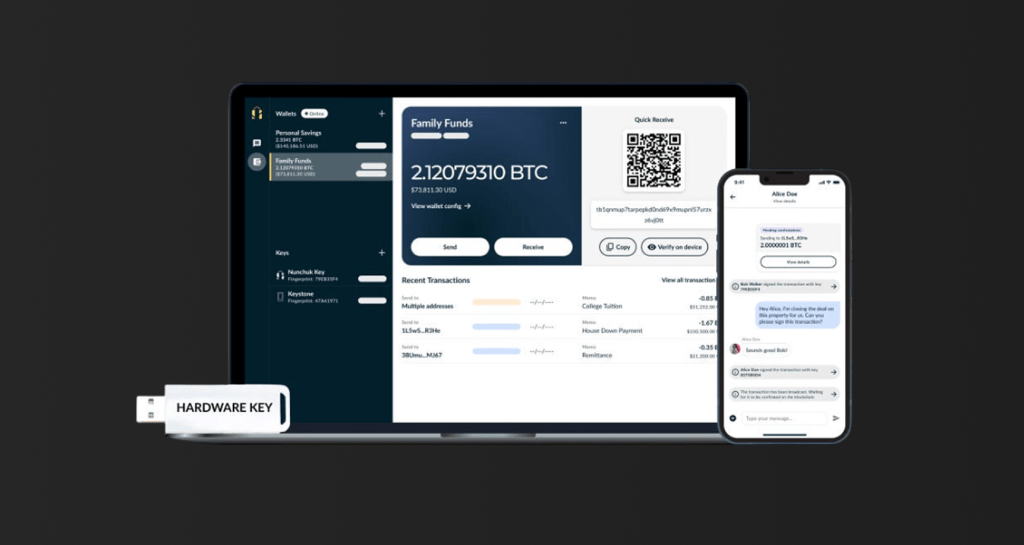
Who it’s for: Advanced users who prioritize long-term storage, inheritance, or collaborative custody while maintaining privacy.
Nunchuk focuses on multisignature (multisig) security but integrates privacy best practices throughout its design. It allows users to set up multiple keys across devices or participants, reducing single points of failure. Privacy is enhanced through coin control, transaction labeling, and the option to connect to self-hosted coordinators and nodes.
Each transaction can route through Tor, ensuring metadata is hidden from external observers. By allowing custom node connections, Nunchuk avoids sending wallet data to centralized servers. Its inheritance planning feature, which lets users set up time-locked key transfers, is handled locally, not through custodial channels.
While it is not a dedicated anonymity wallet like Wasabi, Nunchuk’s structural approach to privacy, isolation, coin control, and controlled information flow, makes it a powerful hybrid tool for users who need both security and discretion. Its continued open-source development and transparent design philosophy have made it popular among long-term Bitcoin holders and self-custody advocates.
Silent.link + Mutiny Wallet Combo (Lightning & No-KYC Layer): Pseudonymous On-Ramp and Lightning Privacy
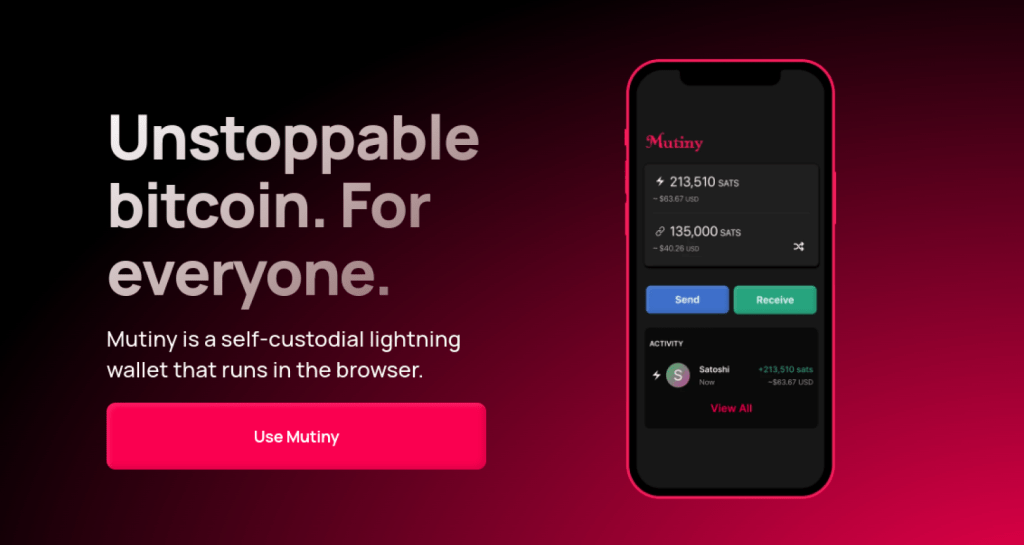
Who it’s for: Users who want to access Bitcoin privately and spend through Lightning without KYC barriers.
Silent.link and Mutiny Wallet form a unique privacy stack that merges no-KYC onboarding with fast, anonymous payments. Silent.link offers anonymous eSIMs and digital payment services that accept Bitcoin onchain or over Lightning. This allows users to obtain phone numbers and communication tools without linking real-world identities to transactions.
Mutiny Wallet, built for the Lightning Network, is a browser-based and mobile-compatible wallet that integrates Tor routing and Nostr connectivity. It focuses on privacy-preserving Lightning payments, allowing users to transact instantly while keeping their identity off the public chain.
Together, these tools enable a near-anonymous mobile payment ecosystem. Users can acquire mobile data or make Lightning payments without traditional KYC intermediaries. The technology is still evolving, and users should verify official domains and avoid unofficial clones.
While early-stage, the Silent.link and Mutiny combination demonstrates the growing intersection between privacy infrastructure and real-world utility. It shows that privacy in crypto is not limited to hiding onchain activity, it can extend to how people connect, communicate, and transact in the digital economy.
Comparison Table: The Best Anonymous Crypto Wallets in 2025
The wallets below represent the most practical balance between privacy, usability, and transparency in 2025. Each applies a different privacy philosophy, from Bitcoin’s CoinJoin mechanisms to Zcash’s shielded proofs and Lightning-based pseudonymity. Choosing between them depends on how much control, mobility, and complexity a user is comfortable managing.
| Wallet | Supported Chains | Key Privacy Tech | Node Options | Open Source | Ideal For |
| Wasabi 2.x | Bitcoin | CoinJoin (WabiSabi), Tor routing | Built-in or custom | Yes | Everyday BTC privacy |
| Sparrow | Bitcoin | PayJoin, Tor, manual CoinJoin | Full-node required | Yes | Advanced users who prefer precision |
| Zashi | Zcash | Shielded transactions, viewing keys | ECC-managed node | Yes | ZEC users who need mobile privacy |
| Nunchuk | Bitcoin | Coin control, multisig, Tor | Optional self-node | Yes | Secure multi-user or inheritance setups |
| Silent.link + Mutiny | Bitcoin (Lightning) | Lightning privacy, Nostr routing | Web-based or Tor | Yes | Mobile users avoiding KYC access |
Each wallet handles privacy differently. Wasabi and Sparrow excel in onchain Bitcoin privacy, though Wasabi automates processes that Sparrow leaves to the user. Zashi relies on cryptographic privacy through zero-knowledge proofs, shielding both addresses and amounts. Nunchuk protects identity indirectly through secure custody structures and Tor integration. Silent.link and Mutiny push privacy toward practical utility, connecting Lightning payments with no-KYC gateways.
Privacy Hygiene: Tools Don’t Replace Discipline
Even the best privacy wallet cannot protect users who lack consistent habits. True anonymity depends on careful behavior, not just software. The right tools lose their power when used carelessly, and a single mistake can reveal a complete transaction history.
Good privacy starts with coin control and smart address management. Every coin carries its own history, and combining private and public funds exposes both. By manually selecting which coins to spend, users can separate clean transactions from identifiable ones. Reusing addresses has the same effect as signing with your name. Generating a new address for every payment keeps your financial trail fragmented and harder to trace.
Network privacy is equally important. Always use Tor or a trusted VPN when connecting your wallet. A visible IP address can link activity across wallets or devices. Running your own node prevents external servers from logging your transaction broadcasts and gives full control over data flow.
Finally, verify every software download. Fake wallet sites and malicious clones have become common phishing tools. Check official repositories, confirm digital signatures, and verify hashes before installing.
No wallet can make you invisible. Once crypto touches a KYC exchange, anonymity ends. Privacy tools only protect you within the decentralized ecosystem. The discipline to use them correctly determines how private you really are.
Monero’s 51% Event: A Lesson in Network Centralization
In August 2025, Monero experienced a major test of its network security when a project called Qubic claimed to control over half of its total mining power. The result was a temporary chain reorganization and several orphaned blocks, leading exchanges such as Kraken to pause Monero deposits. While the event did not expose user data or compromise Monero’s privacy features, it revealed the critical truth that privacy cannot survive without network integrity in decentralized systems.
Monero appears to be in the midst of a successful 51% attack.
The privacy-focused blockchain, launched in 2014 and long targeted by governments and 3-letters agencies, is already banned from most major centralized exchanges.
The Qubic mining pool has been amassing hashrate for…
— Charles Guillemet (@P3b7_) August 12, 2025
Monero’s design still protected transaction anonymity through ring signatures and stealth addresses, but the concentration of mining power showed how even privacy coins can face structural risks. A network controlled by a few entities becomes vulnerable to censorship, double spending, or manipulation, no matter how strong its cryptography may be.
The lesson extends beyond Monero. Privacy wallets, protocols, and zero-knowledge systems rely on a decentralized infrastructure to remain trustworthy. Without sufficient hash rate distribution or validator diversity, even the best privacy tools stand on shaky ground. The Monero incident reminded the crypto community that privacy begins with code but depends on decentralization for survival.
How to Pick the Right Wallet for You
Choosing a privacy wallet is not about which one looks best or promises the most features. It depends on how you use crypto, what risks you face, and how comfortable you are managing your own setup. Each wallet on this list serves a different type of user and threat model.
Start with chain preference. If you operate mainly in Bitcoin, wallets like Wasabi or Sparrow offer the deepest privacy through CoinJoin and PayJoin. If you value zero-knowledge proofs and private balance visibility, Zashi on Zcash provides that layer by default. For fast and low-cost payments, especially through the Lightning Network, Mutiny combined with Silent.link gives flexibility without KYC requirements.
Next, consider device type. Desktop wallets like Wasabi and Sparrow provide granular control and are better suited for long-term storage or large transactions. Mobile wallets such as Zashi, Nunchuk, or Mutiny prioritize convenience and on-the-go privacy, but they depend on how securely you manage your device.
Your threat model matters most. Someone avoiding corporate data profiling will use different tools than someone under financial surveillance. If your concern is exchanges tracking withdrawals, focus on CoinJoin and fresh addresses. If you face political or legal exposure, Tor routing and node independence are essential.
Finally, assess your technical ability. Some wallets automate privacy, while others demand precision and understanding of Bitcoin’s internals. The best choice is the one that you can operate confidently, without shortcuts or confusion. Privacy only works when you control it fully.
Final Thoughts on Anonymous Crypto Wallets in 2025
Privacy in finance is a decision. Every year, more exchanges, governments, and corporations tighten their control over crypto. KYC rules, blockchain analytics, and centralized custody have made transparency unavoidable for most users. Yet financial autonomy still matters, and the ability to transact without surveillance is part of what gave crypto its original purpose. Private wallets preserve that principle.
Keeping part of your holdings in an anonymous or privacy-focused wallet is not about hiding wealth. It is about maintaining independence in an increasingly monitored economy. When your assets sit entirely on custodial platforms, you own nothing but an access key that can be revoked. A self-custodied, privacy-enhanced wallet restores ownership at the protocol level. It lets you decide when, where, and how to interact with the financial system without exposing your entire identity.
In practical terms, privacy wallets offer insurance against future restrictions. Regulations may evolve, and centralized exchanges may impose stricter compliance. But as long as users maintain access to private keys and networks that protect transaction data, they retain the freedom to move value globally. Unlike in banking, where your transactions are private (until authorities get a warrant for any reason), things are different in crypto. You need to protect yourself.
The wallets and tools in this guide, Wasabi, Sparrow, Zashi, Nunchuk, Silent.link, and Mutiny, represent different interpretations of that freedom. Together, they prove that privacy does not mean isolation. It means control, choice, and accountability without exposure. In a world where financial data is more valuable than currency itself, privacy is not an optional feature. It is a modern necessity. Keeping even a portion of your funds in a private wallet is a statement of self-sovereignty, a reminder that financial freedom only exists when it remains in your hands.
Frequently Asked Questions (FAQs)
Are anonymous crypto wallets legal?
Yes, anonymous crypto wallets are legal in most countries. However, using them for illicit activities such as money laundering or tax evasion is illegal. Laws vary by region, so users should follow local compliance rules.
Is Monero private by default and how does that compare to CoinJoin on Bitcoin?
Yes, Monero is private by default, using ring signatures, stealth addresses, and confidential transactions to hide all details. Bitcoin’s CoinJoin provides optional privacy through transaction mixing, but it requires user participation and does not fully conceal sender or receiver information. Nevertheless, there are reports that Monero fell victim to a 51% attack.
Can Zcash shielded transactions still leak data if I misuse viewing keys?
Yes. Sharing or mishandling Zcash viewing keys can reveal shielded transaction details to third parties. Shielded transactions hide amounts and addresses on chain, but viewing keys, node metadata, or network leaks can expose information if you grant access or fail to protect your connections.
Will a privacy wallet make me undetectable to exchanges or tax authorities?
No. Privacy wallets hide onchain data but cannot mask your identity when using KYC exchanges or regulated services. Blockchain analytics, IP logs, and exchange records can still reveal user activity to authorities when required.
Does using Tor slow my wallet down?
Yes. Using Tor can make wallet connections slower because traffic is routed through multiple encrypted relays to protect your IP address. While this adds latency and longer sync times, it significantly increases privacy and prevents third parties from tracking your transactions.
What is PayJoin and when should I use it?
PayJoin is a Bitcoin transaction method where both sender and receiver add inputs, breaking common tracing patterns. Use PayJoin when you want extra privacy in normal payments, as it hides which party initiated the transaction and confuses chain analysis.
Can hardware wallets help with privacy or only with security?
Hardware wallets mainly enhance security by protecting private keys from hacks and malware. However, they can also improve privacy when paired with your own node, since transactions bypass third-party servers that might log your addresses or activity.
How do I avoid fake wallet sites?
Always download wallets from official links listed on verified project pages or GitHub repositories. Check the domain name carefully, verify PGP signatures or file hashes, and avoid links shared on social media, ads, or forums that could lead to phishing clones.




