Annual Crypto Crime Report: Top 5 Countries for Crypto Crime 2022
Summary
- Crypto-associated crime hit an all-time high in 2021 at $14 billion, 0.15% of the total crypto transactions
- North Korea reigns supreme, with crypto crime reaching almost $1.6 billion over 10 years
- The United States is a hotspot for crypto prosecution as well as fraud
- Russia is the world leader in ransomware
- China takes the top spot for total fraud of an estimated $2.3 billion
- The UK is a world leader in crypto money laundering thanks to a lax financial regulatory approach
Crypto crime hotspots
How bad is it?
Crypto crime is widespread. A recent report from blockchain analysis firm Chainalysis found that crypto-associated crime hit an all-time high in 2021. Illicit addresses received $14 billion USD over the course of the year. To keep things in perspective, that’s only 0.15% of the total amount of crypto transactions that year, which reached a record $15.8 trillion. In comparison, the World Economic Forum estimates that proceeds from criminal activity make up 2-5% of the world’s GDP.
Over a decade after the publication of the bitcoin white paper, crypto has gone aboveboard. It’s regulated by major governments and used in mainstream finance. Some spectators, however, still haven’t moved past bitcoin’s early uses as fake internet money used to buy hard drugs off of the Deep Web. Crypto crime is well publicized and often traceable, which might contribute to its outsized criminal reputation.
There’s no denying that the crypto ecosystem has a flourishing criminal underworld. The criminals are diverse: teen basement dwellers, state-backed agents, and hierarchical ransomware gangs.

When it comes to crypto crime, some countries are more prolific than others. North Korea is by far the top ranked country for crypto crime. Skilled hackers in the Hermit Kingdom have raised funds for the country’s weapons programs through a relentless series of profitable cyberattacks. Attacks from the DPRK’s cyber army have targeted governments and private organizations across the world.
The United States comes second thanks to the scale of its underground crypto economy and a series of high-profile scams. U.S. indictments also mean that many crypto crimes are tried under U.S. jurisdiction.
Thanks to the hard work of security professionals around the world, we can confidently say that the sheer amount of ransomware coming out of Russia qualifies it for third place. Ransomware is a particular Russian specialty. Organized gangs of hackers often enjoy tolerance, if not outright employment from the Kremlin.
Large-scale fraud, exchange hacks, and Ponzi schemes mean that China places fourth on Coincub’s crypto crime list. There is also reason to believe that the CCP tolerates some level of crypto crime as long as it aligns with its strategic goals.
Finally, the United Kingdom rounds out the top 5 countries for crypto crime. Lax company registration laws have made it a popular spot for money laundering at scale, and London addresses are often used to give scams an air of legitimacy.
| Country | Rank | Fraud Cases* | Fraud totals in US$ | 2022 GDP Est US$ million | Crypto Fraud relative to 2021 GPD |
| North Korea | 1 | 30 | 1,597,365,000 | 15,847 | 10.08% |
| United States | 2 | 15 | 2,045,349,000 | 22,939,580 | 0.01% |
| Russia * | 3 | 8 | 1,456,900,000 | 1,647,568 | 0.09% |
| China | 4 | 9 | 2,269,521,000 | 16,862,979 | 0.01% |
| United Kingdom | 5 | 13 | 602,011,000 | 3,108,416 | 0.02% |
| Japan | 6 | 6 | 1,241,044,000 | 5,103,110 | 0.02% |
| Hong Kong | 7 | 5 | 586,002,000 | 369,722 | 0.16% |
| Canada | 8 | 5 | 169,729,000 | 2,015,983 | 0.01% |
| British Virgin Islands | 9 | 3 | 103,332,000 | 1,492 | 6.93% |
| Seychelles | 10 | 4 | 65,066,000 | 1,288 | 5.05% |
| South Korea | 11 | 2 | 71,000,000 | 1,823,852 | 0.00% |
| Singapore | 12 | 5 | 45,123,000 | 378,645 | 0.01% |
| Vanuatu | 13 | 2 | 45,253,000 | 999 | 4.53% |
| Poland | 14 | 5 | 29,352,000 | 655,332 | 0.00% |
| New Zealand | 15 | 4 | 12,439,000 | 247,640 | 0.01% |
| Italy | 16 | 2 | 195,303,000 | 2,120,232 | 0.01% |
| Marshall Islands | 17 | 2 | 6,167,000 | 241 | 2.56% |
| Switzerland | 18 | 2 | 32,000,000 | 810,830 | 0.00% |
| Saint Kitts and Nevis | 19 | 2 | 687,000 | 976 | 0.07% |
| Australia | 20 | 2 | 135,000 | 1,610,556 | 0.00% |
| Turkey ** | 21 | 1 | 2,000,000,000 | 795,952 | 0.25% |
| Israel | 22 | 1 | 12,000,000 | 467,532 | 0.00% |
| Finland | 23 | 2 | 31,000 | 296,016 | 0.00% |
| Slovakia | 24 | 1 | 5,000,000 | 116,748 | 0.00% |
| Germany | 25 | 1 | 3,000,000 | 4,230,172 | 0.00% |
| India | 26 | 1 | 3,000,000 | 2,946,061 | 0.00% |
| Malta | 27 | 1 | 3,000,000 | 16,695 | 0.02% |
| Estonia | 28 | 1 | 2,000,000 | 36,039 | 0.01% |
| Gibraltar | 29 | 1 | 2,000,000 | 2,344 | 0.09% |
| Norway | 30 | 1 | 1,000,000 | 445,507 | 0.00% |
| Spain | 31 | 1 | 1,000,000 | 1,439,958 | 0.00% |
| Denmark | 32 | 1 | 600,000 | 396,666 | 0.00% |
| Ireland | 33 | 1 | 570,000 | 516,253 | 0.00% |
| Vietnam | 34 | 1 | 500,000 | 368,002 | 0.00% |
| Brazil | 35 | 1 | 370,000 | 1,645,837 | 0.00% |
| Belize | 36 | 1 | 342,000 | 1,909 | 0.02% |
| Cayman Islands | 37 | 1 | 245,000 | 6,256 | 0.00% |
| Czech Republic | 38 | 1 | 161,000 | 276,914 | 0.00% |
| Panama | 39 | 1 | 51,000 | 60,121 | 0.00% |
| Mongolia | 40 | 1 | 4,000 | 14,280 | 0.00% |
*The ranking counted ransomware strains as single instances of crime, although each ransomware strain may have thousands of individual victims.
** Update 01.07.22: Revised North Korea’s total cases from 15 to 30 in line with Chainalysis report
*** Turkey’s singular $2B case does not highlight the existence of a criminal ecosystem.
1. North Korea
Any discussion of crypto crime by country is going to include North Korea. In the Coincub crypto crime rating, the Hermit Kingdom takes first place by a wide margin. We estimate that North Korea has made $1.59 billion from at least 15 distinct cases of crypto crime that took place between 2017-2022. A staggering 10% of the DPRK’s GDP comes from fraud, theft, and ransomware.
North Korea is in a unique position – nearly all of its cryptocurrency dealings are fraudulent due to comprehensive international sanctions. That has not stopped the Hermit Kingdom from producing some of the world’s most efficient hackers, and some of the most breathtakingly audacious crypto hacks. All of North Korea’s known cryptocurrency business is likely state-sponsored, as internet access is controlled exclusively by Pyongyang.
Ed Caesar, reporting on North Korea’s hacking army for the New Yorker, writes that “North Korea […] is the only nation in the world whose government is known to conduct nakedly criminal hacking for monetary gain.” A 2019 UN security council brief noted that DPRK hacks have shown a marked turn towards revenue generation since 2016, the same year that further sanctions greatly restricted the commodities North Korea could export. It seems like the proceeds of state-sponsored hacks are used to bolster the country’s national defense budget. A UN report claimed that North Korean hackers stole more than $50 million between 2020 and 2021, and launched 7 further attacks on cryptocurrency platforms to help fund their nuclear program.
The DPRK’s cyber program is large and well-organized, with 7,000 employees and operations in over 150 countries. The true extent of North Korea’s contribution to global crypto crime rates is unknown. For every hack attributed to DPRK actors, there are likely many more that will never be solved. Writers at rekt.news, a DeFi journalism platform, wondered how many of the exploits they covered could be attributed to North Korea.
Cryptocurrency is one of the primary sources of internet-based income generation in North Korea. A report by Recorded Future found that the DPRK has been implicated in cryptojacking, exchange thefts, and crypto scams. Cryptojacking refers to the hijacking of a target’s computer to illegally mine cryptocurrency, forcing the victim to unwittingly foot the (often hefty) electricity bill. North Korean hackers targeted South Korean computers with malware that mined the privacy coin Monero (XMR), making a modest profit of $25,000.
When it comes to exchange thefts, North Korea is a juggernaut. The Hermit Kingdom has been implicated in at least 10 separate hacking incidents, with the true number likely much higher. Unlike their ransomware exploits, most North Korean-led exchange hacks are geographically clustered. A UN security council brief concluded that DPRK hackers mostly targeted South Korean exchanges. One exchange, Bithumb, was targeted four separate times, netting the DPRK $60 million.
The Lazarus Group is a North Korean state-backed hacking group that has been behind some of the biggest exploits in the last 10 years, including the infamous Sony hack. They also engineered the infamous WannaCry ransomware strain, which affected 230,000 computers in 150 countries. Researchers at Kaspersky estimate that WannaCry resulted in $4 billion in damages.
Unfortunately, North Korean state-backed hackers are not only talented but also versatile. Several U.S. government agencies warned that North Korean cyber actors have gracefully adapted to Web3 and are now targeting not just centralized crypto exchanges, but “decentralized finance (DeFi) protocols, play-to-earn cryptocurrency video games, cryptocurrency trading companies, venture capital funds[…], and individual holders of large amounts of cryptocurrency or valuable non-fungible tokens (NFTs).”
The U.S. treasury department linked hackers from North Korea’s Lazarus Group to the theft of $620 million worth of crypto from the Ronin blockchain, which supports popular DeFi game Axie Infinity. At the time of writing, the Ronin hack is just about tied with the Poly hack for the largest crypto hack of all time.
It would be one thing if this list was about the percentage of fraud vs legitimate crypto dealings – North Korea would win. What about the number of hacks? According to Chainalysis data, North Korea has over 30 attributed hacks, twice the amount of the next competitor, the US. Kim Jong Un’s dual appreciation for weapons-grade plutonium and imported cheese needs to be funded somehow.
2. United States
The United States is one of the world’s most active crypto economies – in 2021, the Federal Reserve found that 12% of American adults held cryptocurrency. It’s no surprise that it is also home to a high amount of crypto crime. America’s crypto crime statistics are also influenced by its uniquely aggressive approach to prosecuting crypto-enabled crime. U.S. indictments technically mean that many crypto crimes have occurred in U.S. jurisdictions. The U.S. has to be on this ranking because as far as the American government is concerned, most crypto crimes happen in America.
A statement by Assistant Attorney General Kenneth A. Polite Jr. exemplifies the United States’ stance on crypto crime: “Crime, particularly crime involving digital currencies, continues to transcend international boundaries.” A U.S. address is also an attractive way of providing legitimacy to shady crypto scams – there were 26 crypto-related entities falsely claiming to be registered in the United States.
The U.S. isn’t #2 on the ranking solely due to legal technicalities – the country also has a long history of domestically produced crypto-related crime. The infamous dark web market Silk Road allowed users to buy drugs, guns, and other illegal goods with bitcoin. The site operated from February 2011 to October 2013 under the control of Ross Ulbricht, pseudonymously known as the Dread Pirate Roberts. The charges against Ulbricht listed the total revenue generated from sales as 9,519,664 bitcoins. The Silk Road collected 614,305 bitcoin in commissions. At the time, this was worth $1.2 billion and $79.8 million, respectively.
Since the start of 2022, the Department of Justice has publicly announced 12 indictments related to crypto fraud. The biggest story so far has been that of Ilya Lichtenstein and Heather Morgan, a married couple who allegedly conspired to launder $4.5 billion worth of crypto stolen during the 2016 Bitfinex hack. The U.S. is a surprisingly popular place for money laundering – in the first half of 2022 alone, 10 other people were also charged with the crime. It’s no surprise that the U.S. came first in Computer Weekly’s 2022 Money Laundering Hall of Shame, with £216.5bn ($262.34bn) laundered annually.
Delaware corporations are easy to set up and often used for money laundering. In 2013, Brett Wolf reported that a Mt Gox subsidiary called Mutum Sigillum was incorporated in Delaware and acted as an unlicensed money transmitter, in violation of federal law. As a result, the Department of Homeland Security seized more than $5 million from the exchange. This wasn’t the last problem Mt Gox would face. Less than a year later, the exchange lost over 650,000 of their customers’ bitcoins in a breach that still hasn’t been solved.
Many high profile scams have been prosecuted in the US. The most infamous is Bitconnect, a Ponzi scheme that defrauded investors of more than $2 billion. Many people know about Bitconnect from a viral video of promoter Carlos Matos joyfully proselytizing the multi-billion-dollar scam that was subsequently memed into oblivion. The U.S. Justice Department released its indictment for Bitconnect founder Satish Kumbhani in February of 2022.
The U.S. has also been hit by ransomware attacks. On May 7th, 2021, the Colonial Pipeline was hit by a ransomware attack. The attackers, identified as Russian ransomware gang DarkSide, demanded 75 bitcoin ($4.4 million at the time) in return for access to the systems, which the company paid. The pipeline was a crucial piece of infrastructure that supplies gas to much of the Southwestern United States.
The FBI and Cybersecurity and Infrastructure Security Agency (CISA) observed incidents involving ransomware against 14 of the 15 U.S. critical infrastructure sectors. In 2021, the FBI’s Internet Crime Complaint Center (IC3) received 3,729 complaints of ransomware, with adjusted losses estimated at over $49.2 million. The IC3 reported that there were over 466,501 victims of cybercrime in the US, more than anywhere else in the world. In total, victims lost $1.6 billion worth of virtual currency.
So where is most of the ransomware coming from?
3. Russia
Russia takes third place in the Coincub crime ranking due to a thriving ransomware economy and high-profile fraud cases. Russian cybercriminals have generated a whopping $1.4 billion in profit from crypto-related criminal activity, and that’s a conservative estimate. Most of the profit can be attributed to the Conti ransomware, which is estimated to have made anywhere between 180 million and 2.7 billion. Many factors influence the rate of crypto crime in Russia: loose regulation, government-sanctioned impunity (for some), and a tanking economy. That’s not including the heavy sanctions that have been imposed on the country in the wake of the invasion of Ukraine.
According to a Chainalysis report, “Russian cybercriminal organizations are some of the biggest perpetrators of cryptocurrency-based crime — especially ransomware — and local cryptocurrency businesses provide money laundering services that enable this activity.” Most of their activity appears to be financially motivated. In the aftermath of the attack on the Colonial Pipeline, ransomware group DarkSide wrote on their website “our goal is to make money and not creating problems for society.”
According to the Record, Russian hacking groups are careful about who they target. “Many ransomware strains affiliated with Russia and other Eastern European countries have code that prevents them from being deployed against operating systems in detects as being located in a Commonwealth of Independent States (CIS) country — the CIS is an intergovernmental organization of former Soviet states.” A report from Analyst1 found members of Twisted Spider, Viking Spider, Wizard Spider, and LockBit all build checks and balances into their ransomware to ensure the payload does not execute on Russian victims.
In 2021, over 74% of ransomware revenue – over $400 million worth of cryptocurrency – went to strains that Chainalysis deemed highly likely to be affiliated with Russia in some way. Furthermore, blockchain and web traffic data show that most extorted funds are laundered through services that cater primarily to Russian customers. In order to determine whether a ransomware strain is tied to Russia, Chainalysis looks for CIS country avoidance, language, and affiliate location.
Moscow is a significant location for crypto money laundering. Between Q1 of 2019 and Q4 of 2021, 29% to 48% of all funds received by Moscow cryptocurrency businesses were associated with “risky” wallets, or those connote to entities frequently linked to criminal activities – nearly $700 million of crypto from illicit addresses, or 13% of all value received. Between 2019 and 2021, scams made up $313 million of the illicit cryptocurrency sent to Moscow wallets, darknet markets $296 million, and ransomware $38 million.
Contrary to the common image of a grimy criminal underworld, many businesses associated with crypto crime are based in Moscow’s prestigious Federation Tower. An investigation by the New York Times found that many businesses intimately associated with Russia’s crypto criminals were operating in broad daylight from some of the most sought-after real estate in Moscow.
One of them is Suex, a Russia-based OTC broker, which has received millions worth of crypto from wallet addresses associated with criminal activity. In 2021, Suex was sanctioned by the United States Office of Foreign Asset Control for facilitating criminal transactions involving at least 8 different ransomware variants. The Chainalysis crypto crime report 2022 revealed that many of the biggest wallet addresses sending money to Suex are associated with money laundering. Another is EggChange, whose founder Denis Dubnikov was arrested by American authorities in 2021.
Russian ransomware gangs have targeted vital infrastructure in other countries, particularly the US. In the FBI’s Internet Crime Report, it was revealed that strain has a specialty: Conti mostly focused on critical manufacturing, commercial facilities, and agriculture, LockBit victimized government, healthcare, and financial organizations. REvil/Sodinokibi targeted financial services, IT, and healthcare and public health sectors.
It’s not all ransomware – Finiko, a Russia-based Ponzi scheme according to a regional report from Chainalysis, collapsed in July 2021. The scam was headed by Instagram influencer Kirill Doronin. Between December 2019 and August 2021, Finiko received $1.5 billion in bitcoin from 800,000 separate deposits, primarily from users in Russia and Ukraine.
| Ransomware group | Associated strains | Estimated profits |
| DarkSide | DarkSide | $9.12m |
| REvil | REvil/Sodinokibi | $12.13m |
| Wizard Spider | Ryuk Conti | $1.04b |
| Circus Spider | Netwalker/mailto | $27.3m |
| Evil Corp/UNC2165 | LockBit, LockBit 2.0, HADES, WastedLocker, Dridex, Macaw | $100m |
4. China
China takes fourth place, due to the historical profitability of crypto scams as well as a few startling revelations about state-backed operations. According to Coincub’s data, $2.26 billion in revenue has been generated by criminal activity in China, the highest amount of any country.
Exchange hacks tend to get the most publicity, but scams often make more money and fewer headlines. An exchange hack is a singular event that takes a lot of hard work to accomplish. Scams, on the other hand, tend to require less effort and are near-constant background noise in the crypto sphere. The PlusToken scam was one such profitable venture set up in 2018 by Chen Bo. It was structured as a classic Ponzi scheme. The scam grew to over 3,000 layers and had 27 alleged masterminds, with another 82 core members. Local media reported that the scam eventually took over 50 billion yuan ($7.4 billion) worth of cryptocurrency from victims. As of 2020, the Jiangsu Yancheng Intermediate People’s Court has seized over $4 billion in BTC, ETH, XRP, and other cryptocurrencies.
A June report by security researcher Lordx64 for Confiant uncovered a cluster of malicious activity dubbed SeaFlower (藏海花). The apparent objective of SeaFower is to distribute modified web3 wallets with built-in backdoors that grant wallet access to SeaFlower operatives. SeaFlower used sophisticated advertisements perfectly mimicking the actual wallets, luring in unsuspecting users.
SeaFlower targeted users of MetaMask, Coinbase, TokenPocket, and imToken – all wildly popular web3 wallets. MetaMask alone has over 30 million users. The project is incredibly sophisticated to a level not usually seen in the world of crypto hacks, and expensive to run. The culprits are clearly experienced, well-funded, and technically adept. This is something to keep an eye on. In the words lordx64, “SeaFlower is the most technically sophisticated threat targeting web3 users, right after the infamous Lazarus Group.”
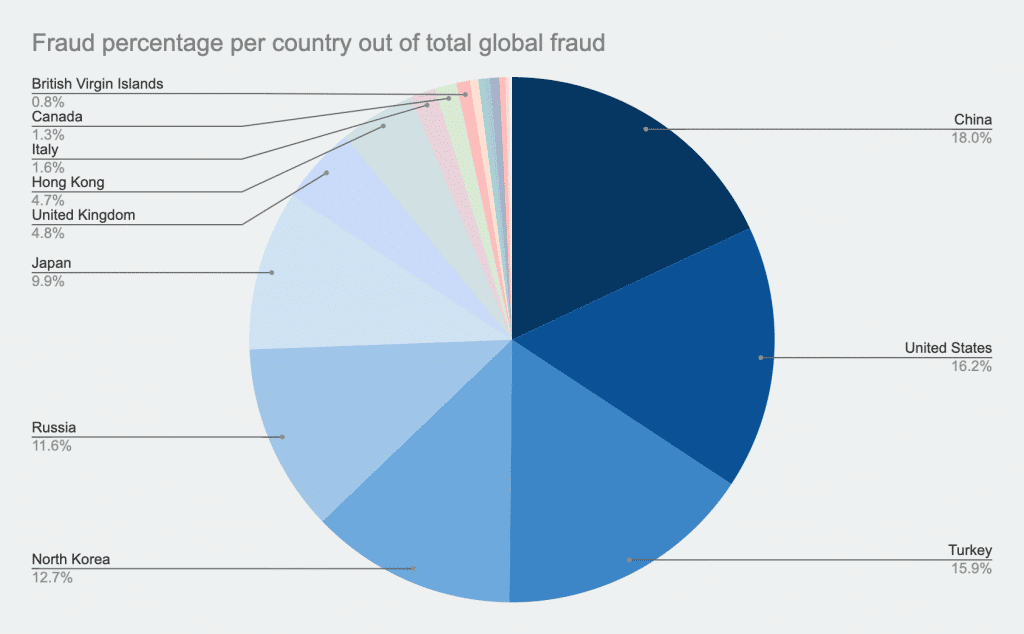
Image source: Coincub
China has an 18% share of the world’s crypto crime volume, with $2.26 billion in illicit proceeds. This tracks, as the Chinese crypto economy is massive – $256 billion in cryptocurrency received between July 2020 and June 2021 alone, despite a strictly enforced recent ban on crypto. in June 2021, following further prohibitions, the Chinese police arrested over 1,100 people from 170 criminal groups suspected of using crypto to launder money.
State-backed espionage groups have been implicated in the deployment of malware and attacks on crypto firms. In 2019, the intelligence company Mandiant published a report on threat actor APT41, which is believed to be a Chinese state-sponsored espionage group. APT41 has targeted healthcare, tech, media, pharmaceuticals, telecoms, travel, and yes, crypto. In 2018, APT41 launched a spear-phishing campaign against a gaming company linked to a cryptocurrency service. In another instance, APT41 attempted to extort a gaming company by deploying Encryptor RaaS ransomware. In another instance, the group compiled an instance of XMRig, a Monero cryptocurrency mining tool.
In addition to their day jobs, members of APT41 have engaged in side-hustle hacks for profit. Mandiant found that the group is unique among China-based actors, as it leverages non-public malware usually reserved for espionage missions for activities that fall outside the scope of traditional state-sponsored missions. Paul Mozur and Chris Buckley, writing for the New York Times, found that Chinese hacking operations can act like “local franchises,” with some engaging in commercial cybercrime on the side. These hackers are paid to work from 9 to 5 for the state – and the CCP isn’t terribly concerned about what they do in their free time.
The top crypto crime countries are often inextricably intertwined with each other. In March, the U.S. Department of Justice indicted two Chinese nationals charged with laundering $100 million worth of cryptocurrency stolen from an exchange by North Korean actors in 2018.
5. United Kingdom
The United Kingdom takes fifth place because of the many hacks and scams that have taken place within its jurisdiction, as well as the legal loopholes that make it easy for criminals to set up business there. The ease of setting up companies in the UK allows fraudsters to engage in elaborate shell games to obfuscate the source and destination of funds. In February, the UK came second in Computer Weekly’s money laundering hall of shame, which estimated that £88bn ($106.6bn) is laundered annually.
Crypto fraud is well-documented in the U.K. In 2021, the U.K. Financial Conduct Authority (FCA) warned that a “significantly high” number of crypto firms failed to meet UK money laundering rules. Between April and September of 2021, the FCA opened more than 300 cases relating to crypto businesses. More than $200m was lost to fraud in the UK that year, and 7,118 cases of crypto fraud were reported. The National Crime Agency’s 2021 National Strategic Assessment of Serious and Organized Crime found that the use of cryptoassets to facilitate money laundering became more popular over lockdown. The use of crypto in general increased across several crime types.
An investigation into a series of scams by The Times revealed insights into how fraudsters use the UK’s lax business regulation to set up scams. Reporter Ali Hussain traced a series of crypto scams back to one individual. All of their firms claimed to operate from exclusive London addresses. Hussain found that entrepreneurs looking to set up a bank do not need to register it with the regulator unless the company has “bank” in its name. Potential fraudsters can register a bank with Companies House without needing to approach a regulator.
In one case, two Manchester-based individuals ran a crypto scam that targeted 150 people from around the world. Victims believed they were depositing money into online savings and trading service that used Binance Smart Chain. When police shut down the operation in 2021, they found $22.25 million worth of crypto stashed on USB sticks.
The UK police have been involved in many other asset seizures. In June of 201, the London Metropolitan Police (Met) seized $158m in crypto during a money-laundering investigation as part of an investigation into global money laundering. The next month, they seized. $250 million worth of crypto. As of January 2022, UK police have seized at least $435 million in illicit crypto.
While some fraudulent companies are not registered in the UK, they do appear to operate from the country. The cryptocurrency trading platform BTC-e was operated by ALWAYS EFFICIENT LP, a company registered in London. In 2017, founder Alexander Vinnik was charged with operating an international money laundering scheme and allegedly laundering funds from the legendary Mt. Gox hack.
Special mentions
– Japan took 6th place. While the country is highly regulated, a prosperous crypto economy has made Japanese exchanges targets for hacks. Mt. Gox ($460m) and Coincheck ($534m), were two of the biggest exchange breaches of all time.
– Hong Kong (7th place) is a global hub for crypto, and played host to several rug-pull projects.
– Canada (8th place) is notably home to the infamous QuadrigaCX debacle, a case so juicy there is now a Netflix documentary about it.
– The British Virgin Islands (9th place) are a hotspot for global corruption and money laundering. Bitfinex, which was hacked and lost $72.3m of customer funds in 2016, was based out of the territory. The total amount lost to fraud is 6.93% of the country’s 2021 GDP.
– Seychelles (10th place) has a reputation as a hotspot for financial crime thanks to lax anti-corruption laws.
Methodology
A taxonomy of crypto crime
We considered 244 instances of crypto crime committed between 2011 and 2022. Instances were collated from the Crystal Blockchain Security Map, Chainalysis yearly crypto crime reports, UN reports, and government documents. When creating the criteria for the top 5 countries for crypto crime, we needed to define what is included under the aegis of crypto crime. We found that the range of criminal activity associated with cryptocurrency is incredibly diverse. You can still buy drugs on the dark web with bitcoin, but it’s also possible to do so much more. The criminal activities included in the ranking include ransomware, fraud, phishing, money laundering, cryptojacking, and theft.
Ransomware
Ransomware is a type of malware that blocks access to data unless a ransom is paid. The most popular ransomware strains demand payment in cryptocurrency. Bitcoin accounted for 98% of ransomware payments in 2019 according to ransomware recovery specialist Coveware. This wasn’t always the case. Over the last decade, the ransomware economy has slowly shifted to using crypto. In the olden days (read: pre-2015), ransoms would be paid via prepaid cards or vouchers, and typically targeted individuals.
When crypto adoption became more widespread, ransomware started shifting to bitcoin as the main payment method. This took time, and the process wasn’t always easy. Early crypto ransomware notes would even contain step-by-step instructions on how to get bitcoin. The shift from gift cards to crypto came at around the time ransomware shifted from individuals to enterprise. The Chainalysis crypto crime report 2022 found that the average ransom payment in 2021 was $118,000 – not a sum that most people could pay by themselves.

Image courtesy of Wikipedia
When it came down to it, cryptocurrency was easier to scale when hunting big game, i.e. large corporations, hospitals, and vital public utilities. After all, it would be difficult to buy $100,000 in iTunes gift cards. Ironically, ransomware gangs have sophisticated methods of laundering traditional finance, but have a much harder time with bitcoin.
Why bitcoin? According to security experts, most ransomware gangs exclusively use bitcoin out of convenience. Onboarding victims to altcoins was too difficult, and the parties targeted couldn’t figure out how to buy Monero (XMR), a privacy-oriented coin and a favorite for money laundering.
One of the biggest strains of ransomware is Conti, which has extorted anywhere from $180 million to $2.7 billion in cryptocurrency over two years, depending on who you ask. The biggest exporter of ransomware is Iran, with 21 documented strains. The most influential exporter of ransomware is Russia. The 16 documented strains of Russian ransomware have netted hundreds of millions of dollars while causing untold amounts of havoc around the world. State-backed Russian ransomware gangs have been implicated in financially and politically motivated attacks.
Chainalysis estimated that $602 million was paid out to ransomware gangs in 2022, though the actual figure is most likely much higher. In June, officials from the American Department of Justice revealed that only 25% of the victims of Netwalker ransomware reported incidents.
Targets of successful ransomware attacks are often reluctant to come forward and report crypto crime. During a talk in 2022, Carlton Gammons, the lead prosecutor for the U.S. Attorney’s Office for the Middle District of Florida, said that “[companies] did not want their shareholders, or customers to know that they were victims of ransomware. They’d rather do whatever they’re going to want to do internally rather than let anybody find out that they’ve been victimized.”
Scams
Crypto scams are many and varied, which may be why they were the most profitable type of crypto crime in 2021. Chainalysis estimates scamming revenue at $7.8 billion. Rug pulls were the most common type of scam, making fraudsters $2.6 billion. We considered exit scams/rug pulls, Ponzi schemes, romance scams, and phishing in our ranking.
Theft
Good old theft. While other crypto crimes need long explainers and glossaries, theft is a no-brainer. In 2021, $3.2 billion worth of cryptocurrency was stolen, with the majority ($2.2 billion) taken from DeFi protocols.
Ranking limitations
Crypto is geographically dispersed, and it’s not easy to accurately pin blame on the culprits. In cases where the perpetrators were not identifiable, we attribute the crime to the country of origin. In other cases, it was not possible to identify the geography of the perpetrator or the victim. Of the 244 cases of crypto-related crime we studied, 100 were unattributable. This ranking is designed to provide an overview of a country’s engagement in the global economy of crypto crime, whether as a victim or perpetrator. In order to provide a sense of proportion, we compared crypto crime proceeds to a given country’s GDP for 2021.
Known association with crypto criminals automatically nets a higher ranking. The problem is that attribution of crypto crime is incredibly difficult. If scammers and fraudsters are any good, we don’t know where they operate from. The Coincub crypto crime ranking primarily focused on attacks that target institutions and groups. For example, the WannaCry ransomware is counted as one instance, as opposed to 200,000. The actual scale of crypto crime far exceeds 244 victims in 12 years. However, most victims do not come forward, making it difficult to get an accurate handle on the true amount of crypto-related criminal activity in a given country.
Crypto crime has the unusual distinction of being relatively easy to trace. Blockchain applications lend themselves to forensics, as all information is public and preserved. Public-facing blockchains, such as the ones that support bitcoin and ethereum, can be analyzed to reveal the flow of money from wallet to wallet. It’s important to note that bitcoin and most crypto is pseudonymous, not anonymous. If a wallet is known to be linked to criminal activity, it’s possible to track every single transaction it participates in.
Ranking countries for crypto crime is tricky. Anonymity, jurisdiction-hopping, and multinational criminal efforts can make attribution of a given instance of fraud almost impossible. However, careful analysis by security professionals and blockchain forensics experts has provided insight into the geography of crypto crime.
FAQs
What is phishing?
Phishing refers to an attempt by attackers to trick victims into divulging sensitive information or performing actions on their behalf. Phishing attacks are frequently targeted, and cleverly designed to get victims to perform the desired action. Attacks can result in the theft of valuable data or the installation of malware and/or ransomware.
Spear phishing specifically refers to sophisticated phishing methods that target specific individuals or groups within an organization. Spear phishing attacks often involve emails with attachments that contain malicious code. The emails themselves are written to encourage the victim to open the attachment, therefore giving the attacker access to their computer.
What is ransomware-as-a-service (RaaS)?
Ransomware-as-a-service (RaaS) is a category of criminal business model in which one group manufactures ransomware, and outsources its distribution to affiliates. For example, the Conti group writes the malware that encrypts files and provides a service where affiliates can work for them by hacking computers and installing malware. In return, affiliates get a cut of the ransom. According to Crowdstrike, RaaS kits can include 24/7 support, user reviews, and forums.
How can you protect yourself from crypto crime?
Platform security
- Use a password manager
- Use two-factor authentication for all of your accounts
- Never reuse passwords
- Check https://haveibeenpwned.com/ frequently to see if one of your accounts was involved in a breach
- Use cold wallets to store the majority of your crypto
Protecting against fraud
- Check the reputation of whatever service you’re using. Be aware that you can’t always trust social media due to spam bots.
- Only scammers guarantee quick and easy profits. If it sounds too good to be true, it is
- Romance scams are increasingly common. If you’re dating someone online, don’t listen to any investment advice they give you
- Celebrity endorsements are easily faked
- No one is going to double your bitcoin. Absolutely no one
- Do not trust financial advisors that contact you first, especially on social media
Defend against phishing
- Verify the sender of an email before clicking on any links
- Do not click links of download attachments in emails from unknown sources
- Be wary of unsolicited emails
- Hackers will often try to manufacture a sense of urgency to get you to perform rash actions. If an email calls for immediate action, be on your guard
- Do not enter personal information or passwords into any websites or forms you cannot trust
Reading list
General
Crypto Scams Have Cost Consumers More Than $1 Billion, FTC Says | CNET
The Chainalysis Crypto Crime Report 2022
The Chainalysis Crypto Crime Report 2021
Cryptocurrency Crime and Anti-Money Laundering Report, February 2021 | CipherTrace
Explaining prosecution outcomes for cryptocurrency-based financial crimes | UCL Discovery
Cryptocurrency buzz drives record investment scam losses | Federal Trade Commission
Crypto Romance Scams: Don’t Fall for These Dating App Swindlers | Coindesk
US Courts Are Coming After Crypto Exchanges That Skirt Sanctions | WIRED UK
The Perfect Weapon: war, sabotage, and fear in the cyber age | David E. Sanger
North Korea
How North Korea Revolutionized the Internet as a Tool for Rogue Regimes | Recorded Future
United Nations Security Council Report S/2019/691 [PDF]
Significant Cyber Incidents Since 2006 | CSIS [PDF]_
What is WannaCry ransomware? | Kaspersky
2021 Internet Crime Report | IC3 [PDF]
Trellix Threat Labs Research Report: April 2022
Inside Conti leaks: The Panama Papers of ransomware | The Record
Evil Corp Switches to Ransomware-as-a-Service to Evade US Sanctions | PCMag
LockBit 2.0: How This RaaS Operates and How to Protect Against It | Unit 42
Indicators of Compromise Associated with LockBit 2.0 Ransomware | IC3
LockBit RaaS In-Depth Analysis | Prodaft
Treasury Sanctions Evil Corp, the Russia-Based Cybercriminal Group Behind Dridex Malware | U.S. Department of the Treasury
APT41, A Dual Espionage and Cyber Crime Operation | Mandiant [PDF]
National Strategic Assessment of Serious and Organised Crime 2021 | National Crime Agency [PDF]
Financial Conduct Authority investigated 300 UK crypto firms last year | Financial Times
Over $200M Lost to Crypto Fraud in the UK This Year | Coindesk
Acknowledgments
We would like to acknowledge the work of the following writers and researchers, without which this report would not be possible: Crystal Blockchain, Chainalysis, Mandiant, the Record, ransomwhe.re, Confiant, and many others.




 UAE
UAE  Canada
Canada